利用openssl自制ca证书以及ssl证书
搞一个steam社区的本地反带,搞了一天
前提安装openssl" title="openssl">openssl
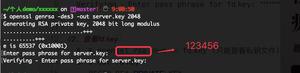
server私钥openssl genrsa -out server.key 1024
server公钥
openssl rsa -in server.key -pubout -out server.pem
client私钥
openssl genrsa -out client.key 1024
client公钥
openssl rsa -in client.key -pubout -out client.pem
注册ca,让自己变成注册商,自签证书后导入到可信任证书
ca私钥
openssl genrsa -out ca.key 1024
自签证书
openssl req -config openssl.cnf -key ca.key -new -x509 -days 3650 -sha256 -extensions v3_ca -out ca.crt
制作服务器私钥,和请求文件
私钥
openssl genrsa -out server.key 1024
私钥请求文件
openssl req -config openssl.cnf -new -key server.key -out server.csr
echo 00 > serial | copy nul index.txt
用请求文件到ca签发,生成ca_server.crt
ca签发
openssl ca -config openssl.cnf -extensions server_cert -days 3650 -md sha256 -in server.csr -out ca_server.crt
系统已经有了你的ca机构证书,所以服务器证书就会被认为是正规ca机构签发的
最后用server.keyg和ca_server.crt
openssl.cnf
[ ca ]# `man ca`
default_ca = CA_default
[ CA_default ]
# Directory and file locations.
dir = C:/Users/Administrator/Desktop/certs #这里改成实际目录
certs = $dir/certs
crl_dir = $dir/crl
new_certs_dir = $dir/newcerts
database = $dir/index.txt
serial = $dir/serial
RANDFILE = $dir/private/.rand
# The root key and root certificate.
private_key = $dir/ca.key
certificate = $dir/ca.crt
# For certificate revocation lists.
crlnumber = $dir/crlnumber
crl = $dir/crl/ca.crl.pem
crl_extensions = crl_ext
default_crl_days = 30
# SHA-1 is deprecated, so use SHA-2 instead.
default_md = sha256
name_opt = ca_default
cert_opt = ca_default
default_days = 375
preserve = no
policy = policy_strict
[ policy_strict ]
# The root CA should only sign intermediate certificates that match.
# See the POLICY FORMAT section of `man ca`.
countryName = match
stateOrProvinceName = match
organizationName = match
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
[ policy_loose ]
# Allow the intermediate CA to sign a more diverse range of certificates.
# See the POLICY FORMAT section of the `ca` man page.
countryName = optional
stateOrProvinceName = optional
localityName = optional
organizationName = optional
organizationalUnitName = optional
commonName = supplied
emailAddress = optional
[ req ]
# Options for the `req` tool (`man req`).
default_bits = 2048
distinguished_name = req_distinguished_name
string_mask = utf8only
# SHA-1 is deprecated, so use SHA-2 instead.
default_md = sha256
# Extension to add when the -x509 option is used.
x509_extensions = v3_ca
req_extensions = v3_req
[ req_distinguished_name ]
# See <https://en.wikipedia.org/wiki/Certificate_signing_request>.
countryName = Country Name (2 letter code)
stateOrProvinceName = State or Province Name
localityName = Locality Name
0.organizationName = Organization Name
organizationalUnitName = Organizational Unit Name
commonName = Common Name
emailAddress = Email Address
# Optionally, specify some defaults.
countryName_default = CN
stateOrProvinceName_default = HeBei
localityName_default = BaoDing
0.organizationName_default = ShanYou
organizationalUnitName_default = ShanYou
commonName_default = ShanYou
emailAddress_default = mail@shanyou.ltd
[ v3_req ]
# Extensions to add to a certificate request
basicConstraints = CA:FALSE
keyUsage = nonRepudiation, digitalSignature, keyEncipherment
subjectAltName = @alt_names
[ alt_names ]
DNS.1 = steamcommunity.com #这里修改为你的映射网址(hosts我修改为"我的ip地址 www.word.com")
DNS.2 = *.steamcommunity.com
[ v3_ca ]
# Extensions for a typical CA (`man x509v3_config`).
subjectKeyIdentifier = hash
authorityKeyIdentifier = keyid:always,issuer
basicConstraints = critical, CA:true
keyUsage = critical, digitalSignature, cRLSign, keyCertSign
[ v3_intermediate_ca ]
# Extensions for a typical intermediate CA (`man x509v3_config`).
subjectKeyIdentifier = hash
authorityKeyIdentifier = keyid:always,issuer
basicConstraints = critical, CA:true, pathlen:0
keyUsage = critical, digitalSignature, cRLSign, keyCertSign
[ usr_cert ]
# Extensions for client certificates (`man x509v3_config`).
basicConstraints = CA:FALSE
nsCertType = client, email
nsComment = "OpenSSL Generated Client Certificate"
subjectKeyIdentifier = hash
authorityKeyIdentifier = keyid,issuer
keyUsage = critical, nonRepudiation, digitalSignature, keyEncipherment
extendedKeyUsage = clientAuth, emailProtection
[ server_cert ]
# Extensions for server certificates (`man x509v3_config`).
basicConstraints = CA:FALSE
nsCertType = server
nsComment = "OpenSSL Generated Server Certificate"
subjectKeyIdentifier = hash
authorityKeyIdentifier = keyid,issuer:always
keyUsage = critical, digitalSignature, keyEncipherment
extendedKeyUsage = serverAuth
subjectAltName = @alt_names
[ crl_ext ]
# Extension for CRLs (`man x509v3_config`).
authorityKeyIdentifier=keyid:always
[ ocsp ]
# Extension for OCSP signing certificates (`man ocsp`).
basicConstraints = CA:FALSE
subjectKeyIdentifier = hash
authorityKeyIdentifier = keyid,issuer
keyUsage = critical, digitalSignature
extendedKeyUsage = critical, OCSPSigning
以上是 利用openssl自制ca证书以及ssl证书 的全部内容, 来源链接: utcz.com/z/267747.html