etcd节点扩容至两个节点
本文内容纲要:etcd节点扩容至两个节点
本篇已经安装了单个etcd,然后进行扩容etcd节点至2个,安装单节点请参照:https://www.cnblogs.com/effortsing/p/10295261.html实验架构
test1: 192.168.0.91 etcd
test2: 192.168.0.92 etcd
test3: 192.168.0.93 无
需求:test1节点已经安装了etcd, 现在要把test2节点作为etcd节点添加进来
1、环境配置
# 如下操作在所有节点操作
修改主机名
# 注意修改 各自节点对应的 主机名
sed -i '$a\hostname=test2' /etc/hostname
sed -i '$a\hostname=test2' /etc/sysconfig/network && hostnamectl set-hostname test2
配置hosts解析
cat >>/etc/hosts<<EOF
192.168.0.91 test1
192.168.0.92 test2
192.168.0.93 test3
EOF
禁用selinux
sed -i 's/SELINUX=permissive/SELINUX=disabled/' /etc/sysconfig/selinux
sed -i 's/enforcing/disabled/g' /etc/selinux/config
关闭swap
# 注释/etc/fstab文件里swap相关的行
sed -i 's/\/dev\/mapper\/centos-swap/#\/dev\/mapper\/centos-swap/g' /etc/fstab
关掉防火墙
systemctl stop firewalld && systemctl disable firewalld
都退出xshell查看主机名
开启forward
iptables -P FORWARD ACCEPT
配置转发相关参数
cat >> /etc/sysctl.d/k8s.conf <<EOF
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
vm.swappiness=0
EOF
加载系统参数
sysctl --system
加载ipvs相关内核模块
如果重新开机,需要重新加载
modprobe ip_vs
modprobe ip_vs_rr
modprobe ip_vs_wrr
modprobe ip_vs_sh
modprobe nf_conntrack_ipv4
lsmod | grep ip_vs
安装etcd
useradd etcd
mkdir -p /server/software/k8s
mkdir -p /opt/k8s/bin
cd /server/software/k8s
wget https://github.com/coreos/etcd/releases/download/v3.2.18/etcd-v3.2.18-linux-amd64.tar.gz
tar -xf etcd-v3.2.18-linux-amd64.tar.gz
mv etcd-v3.2.18-linux-amd64/etcd* /opt/k8s/bin
chmod +x /opt/k8s/bin/*
ln -s /opt/k8s/bin/etcd /usr/bin/etcd
ln -s /opt/k8s/bin/etcdctl /usr/bin/etcdctl
etcd --version
2、复制test1单节点ca证书和私钥、etcd证书和私钥
test2 上先创建存放证书和私钥目录
mkdir -p /etc/kubernetes/cert/
mkdir -p /etc/etcd/cert/
从test1节点上找到证书复制过来
scp /etc/kubernetes/cert/ca*.pem root@192.168.0.92:/etc/kubernetes/cert/
scp /etc/etcd/cert/etcd*.pem root@192.168.0.92:/etc/etcd/cert/
chmod 777 /etc/etcd/cert/*
chmod 777 /etc/kubernetes/*
3、添加证书到linux系统受信任列表(选做)
添加根证书到linux系统受信任列表
cd /etc/kubernetes/cert/
cat ca.pem >> /etc/pki/tls/certs/ca-bundle.crt
添加etcd 证书到linux系统受信任列表
cd /etc/etcd/cert/
cat etcd.pem >> /etc/pki/tls/certs/ca-bundle.crt
5、添加新成员
5.1、注册新节点
# 在test1节点上操作
# etcdctl 在注册完新节点后,会返回一段提示,包含3个环境变量,需要在etcd启动脚本中修改成这3个环境变量
[root@test1 ~]# etcdctl --ca-file /root/ssl/ca.pem --cert-file /root/ssl/etcd.pem --key-file /root/ssl/etcd-key.pem member add test2 http://192.168.0.92:2380
Added member named test2 with ID 2eb21869c9f27e29 to cluster
ETCD_NAME="test2"
ETCD_INITIAL_CLUSTER="test2=http://192.168.0.92:2380,test1=https://192.168.0.91:2380"
ETCD_INITIAL_CLUSTER_STATE="existing"
5.2、修改test2节点的peer url为https
etcdctl --ca-file /etc/kubernetes/cert/ca.pem --cert-file /etc/etcd/cert/etcd.pem --key-file /etc/etcd/cert/etcd-key.pem member update test2 https://192.168.0.92:2380
如果执行失败,先跳过,不影响
6、 配置环境变量
# 在 test2 节点上操作
cat >> /etc/profile << EOF
export ETCD_NAME=$(hostname)
export INTERNAL_IP=$(hostname -i | awk '{print $NF}')
export ECTD_CLUSTER='test1=https://192.168.0.91:2380'
EOF
source /etc/profile
7、配置启动脚本
# 在 test2 节点操作
# 把第5 步 生成的结果写到 etcd启动脚本中,
mkdir -p /data/etcd
cat> /etc/systemd/system/etcd.service<< EOF
[Unit]
Description=Etcd Server
After=network.target
After=network-online.target
Wants=network-online.target
Documentation=https://github.com/coreos
[Service]
Type=notify
WorkingDirectory=/data/etcd
EnvironmentFile=-/etc/etcd/etcd.conf
ExecStart=/opt/k8s/bin/etcd \
--name ${ETCD_NAME} \
--cert-file=/etc/etcd/cert/etcd.pem \
--key-file=/etc/etcd/cert/etcd-key.pem \
--peer-cert-file=/etc/etcd/cert/etcd.pem \
--peer-key-file=/etc/etcd/cert/etcd-key.pem \
--trusted-ca-file=/etc/kubernetes/cert/ca.pem \
--peer-trusted-ca-file=/etc/kubernetes/cert/ca.pem \
--initial-advertise-peer-urls https://${INTERNAL_IP}:2380 \
--listen-peer-urls https://${INTERNAL_IP}:2380 \\
--listen-client-urls https://${INTERNAL_IP}:2379,http://127.0.0.1:2379 \
--advertise-client-urls https://${INTERNAL_IP}:2379 \
--initial-cluster-token my-etcd-token \
--initial-cluster $ECTD_CLUSTER,test2=http://192.168.0.92:2380 \
--initial-cluster-state existing \
--data-dir=/data/etcd
Restart=on-failure
RestartSec=5
LimitNOFILE=65536
[Install]
WantedBy=multi-user.target
EOF
8、启动新节点
systemctl daemon-reload #一定要执行,否则报错
systemctl start etcd
systemctl status etcd
systemctl enable etcd
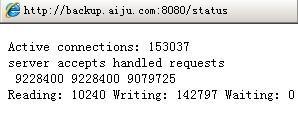
9、查看集群成员和安全状态
# 在test1节点上操作
[root@test1 ~]# etcdctl --ca-file /etc/kubernetes/cert/ca.pem --cert-file /etc/etcd/cert/etcd.pem --key-file /etc/etcd/cert/etcd-key.pem member list
2eb21869c9f27e29: name=test2 peerURLs=http://192.168.0.92:2380 clientURLs=https://192.168.0.92:2379 isLeader=false
42f7141ed6110de1: name=test1 peerURLs=https://192.168.0.91:2380 clientURLs=https://192.168.0.91:2379 isLeader=true
[root@test1 ~]# etcdctl --ca-file /etc/kubernetes/cert/ca.pem --cert-file /etc/etcd/cert/etcd.pem --key-file /etc/etcd/cert/etcd-key.pem cluster-health
member 2eb21869c9f27e29 is healthy: got healthy result from https://192.168.0.92:2379
member 42f7141ed6110de1 is healthy: got healthy result from https://192.168.0.91:2379
cluster is healthy
9.2、修改所有节点启动文件一致,然后重启
报错解决:
[root@test2 k8s]# etcdctl --ca-file /etc/kubernetes/cert/ca.pem --cert-file /etc/etcd/cert/etcd.pem --key-file /etc/etcd/cert/etcd-key.pem member list
Error: client: etcd cluster is unavailable or misconfigured; error #0: dial tcp 127.0.0.1:4001: getsockopt: connection refused
; error #1: dial tcp 127.0.0.1:2379: getsockopt: connection refused
error #0: dial tcp 127.0.0.1:4001: getsockopt: connection refused
error #1: dial tcp 127.0.0.1:2379: getsockopt: connection refused
启动文件需要添加:
http://127.0.0.1:2379
其他报错,删除etcd数据目录重启
本文内容总结:etcd节点扩容至两个节点
原文链接:https://www.cnblogs.com/effortsing/p/10296424.html
以上是 etcd节点扩容至两个节点 的全部内容, 来源链接: utcz.com/z/297040.html