使用JSch跳过Kerberos身份验证提示
我Connect()在Ssh下面的Java类中使用该方法,以便使用SSH(JSch)连接到服务器并在服务器中运行命令。
问题在于,运行Connect()服务器时,提示下一条消息:
Kerberos username [********]:Kerberos password for ********:
为了继续运行,我需要手动按Enter两次键,一次为用户名,另一次为密码。我试图添加下一个代码:
// Press ENTERRobot r = new Robot();
r.keyPress(KeyEvent.VK_ENTER);
r.keyRelease(KeyEvent.VK_ENTER);
但是此代码仅适用于用户名,当服务器要求输入密码时,我无法弄清楚如何自动按Enter。到目前为止,我已经尝试将另一个代码段放在下面的上方。
session.connect();线。
package ConnectSSH;import java.awt.Robot;
import java.awt.event.KeyEvent;
import java.io.*;
import com.jcraft.jsch.ChannelExec;
import com.jcraft.jsch.JSch;
import com.jcraft.jsch.Session;
import com.jcraft.jsch.UserInfo;
public class Ssh{
private static final String user = "********";
private static final String host = "********";
private static final Integer port = 22;
private static final String pass = "********";
public void Connect() throws Exception{
JSch jsch = new JSch();
Session session = jsch.getSession(user, host, port);
UserInfo ui = new SUserInfo(pass, null);
session.setUserInfo(ui);
session.setPassword(pass);
//Press ENTER
Robot r = new Robot();
r.keyPress(KeyEvent.VK_ENTER);
r.keyRelease(KeyEvent.VK_ENTER);
session.connect();
ChannelExec channelExec = (ChannelExec)session.openChannel("exec");
InputStream in = channelExec.getInputStream();
channelExec.setCommand("RUN COMMAND");
channelExec.connect();
BufferedReader reader = new BufferedReader(new InputStreamReader(in));
String linea = null;
int index = 0;
while ((linea = reader.readLine()) != null) {
System.out.println(++index + " : " + linea);
}
channelExec.disconnect();
session.disconnect();
}
}
这是SUserInfo班级
package ConnectSSH;import com.jcraft.jsch.UserInfo;
public class SUserInfo implements UserInfo {
private String password;
private String passPhrase;
public SUserInfo (String password, String passPhrase) {
this.password = password;
this.passPhrase = passPhrase;
}
public String getPassphrase() {
return passPhrase;
}
public String getPassword() {
return password;
}
public boolean promptPassphrase(String arg0) {
return true;
}
public boolean promptPassword(String arg0) {
return false;
}
public boolean promptYesNo(String arg0) {
return true;
}
public void showMessage(String arg0) {
System.out.println("SUserInfo.showMessage()");
}
}
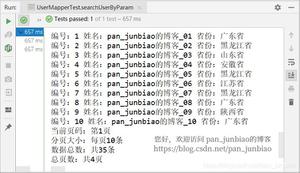
这是记录器返回的内容:
INFO: Connecting to ****** port 22INFO: Connection established
INFO: Remote version string: SSH-2.0-Sun_SSH_1.1.2
INFO: Local version string: SSH-2.0-JSCH-0.1.52
INFO: CheckCiphers: aes256-ctr,aes192-ctr,aes128-ctr,aes256-cbc,aes192-cbc,aes128-cbc,3des-ctr,arcfour,arcfour128,arcfour256
INFO: aes256-ctr is not available.
INFO: aes192-ctr is not available.
INFO: aes256-cbc is not available.
INFO: aes192-cbc is not available.
INFO: CheckKexes: diffie-hellman-group14-sha1,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521
INFO: diffie-hellman-group14-sha1 is not available.
INFO: CheckSignatures: ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521
INFO: SSH_MSG_KEXINIT sent
INFO: SSH_MSG_KEXINIT received
INFO: kex: server: gss-group1-sha1-toWM5Slw5Ew8Mqkay+al2g==,diffie-hellman-group-exchange-sha1,diffie-hellman-group1-sha1
INFO: kex: server: ssh-rsa,ssh-dss
INFO: kex: server: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc,aes192-ctr,aes192-cbc,aes256-ctr,aes256-cbc
INFO: kex: server: aes128-ctr,aes128-cbc,arcfour,3des-cbc,blowfish-cbc,aes192-ctr,aes192-cbc,aes256-ctr,aes256-cbc
INFO: kex: server: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
INFO: kex: server: hmac-md5,hmac-sha1,hmac-sha1-96,hmac-md5-96
INFO: kex: server: none,zlib
INFO: kex: server: none,zlib
INFO: kex: server: ar-EG,ar-SA,bg-BG,ca-ES,cs-CZ,da-DK,de,de-AT,de-CH,de-DE,de-LU,el-CY,el-GR,en-AU,en-CA,en-GB,en-IE,en-MT,en-NZ,en-US,es,es-AR,es-BO,es-CL,es-CO,es-CR,es-EC,es-ES,es-GT,es-MX,es-NI,es-PA,es-PE,es-PY,es-SV,es-UY,es-VE,et-EE,fi-FI,fr,fr-BE,fr-CA,fr-CH,fr-FR,fr-LU,he-IL,hi-IN,hr-HR,hu-HU,is-IS,it,it-IT,ja-JP,kk-KZ,ko,ko-KR,lt-LT,lv-LV,mk-MK,mt-MT,nb-NO,nl-BE,nl-NL,nn-NO,pl,pl-PL,pt-BR,pt-PT,ro-RO,ru,ru-RU,sh-BA,sk-SK,sl-SI,sq-AL,sr-CS,sv,sv-SE,th-TH,tr-TR,uk-UA,zh,zh-CN,zh-HK,zh-TW,ar,ca,cz,da,el,et,fi,he,hu,ja,lt,lv,nl,no,no-NO,no-NY,nr,pt,sr-SP,sr-YU,th,tr,i-default
INFO: kex: server: ar-EG,ar-SA,bg-BG,ca-ES,cs-CZ,da-DK,de,de-AT,de-CH,de-DE,de-LU,el-CY,el-GR,en-AU,en-CA,en-GB,en-IE,en-MT,en-NZ,en-US,es,es-AR,es-BO,es-CL,es-CO,es-CR,es-EC,es-ES,es-GT,es-MX,es-NI,es-PA,es-PE,es-PY,es-SV,es-UY,es-VE,et-EE,fi-FI,fr,fr-BE,fr-CA,fr-CH,fr-FR,fr-LU,he-IL,hi-IN,hr-HR,hu-HU,is-IS,it,it-IT,ja-JP,kk-KZ,ko,ko-KR,lt-LT,lv-LV,mk-MK,mt-MT,nb-NO,nl-BE,nl-NL,nn-NO,pl,pl-PL,pt-BR,pt-PT,ro-RO,ru,ru-RU,sh-BA,sk-SK,sl-SI,sq-AL,sr-CS,sv,sv-SE,th-TH,tr-TR,uk-UA,zh,zh-CN,zh-HK,zh-TW,ar,ca,cz,da,el,et,fi,he,hu,ja,lt,lv,nl,no,no-NO,no-NY,nr,pt,sr-SP,sr-YU,th,tr,i-default
INFO: kex: client: diffie-hellman-group1-sha1,diffie-hellman-group-exchange-sha1,diffie-hellman-group-exchange-sha256,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521
INFO: kex: client: ssh-rsa,ssh-dss,ecdsa-sha2-nistp256,ecdsa-sha2-nistp384,ecdsa-sha2-nistp521
INFO: kex: client: aes128-ctr,aes128-cbc,3des-ctr,3des-cbc,blowfish-cbc
INFO: kex: client: aes128-ctr,aes128-cbc,3des-ctr,3des-cbc,blowfish-cbc
INFO: kex: client: hmac-md5,hmac-sha1,hmac-sha2-256,hmac-sha1-96,hmac-md5-96
INFO: kex: client: hmac-md5,hmac-sha1,hmac-sha2-256,hmac-sha1-96,hmac-md5-96
INFO: kex: client: none
INFO: kex: client: none
INFO: kex: client:
INFO: kex: client:
INFO: kex: server->client aes128-ctr hmac-md5 none
INFO: kex: client->server aes128-ctr hmac-md5 none
INFO: SSH_MSG_KEXDH_INIT sent
INFO: expecting SSH_MSG_KEXDH_REPLY
INFO: ssh_rsa_verify: signature true
WARN: Permanently added '********' (RSA) to the list of known hosts.
INFO: SSH_MSG_NEWKEYS sent
INFO: SSH_MSG_NEWKEYS received
INFO: SSH_MSG_SERVICE_REQUEST sent
INFO: SSH_MSG_SERVICE_ACCEPT received
INFO: Authentications that can continue: gssapi-with-mic,publickey,keyboard-interactive,password
INFO: Next authentication method: gssapi-with-mic
然后显示下一条消息
Kerberos username [******]: Kerberos password for ********:其中Enter关键是通过机器人的用户名自动按下,但Enter需要从键盘按下密码密钥。
回答:
您已经将Kerberos /GSSAPI身份验证设置为首选身份验证,但是您似乎并没有实际使用/想要它。由于您没有为Kerberos提示指定任何用户名或密码。
解决方案是gssapi-with-mic从首选身份验证方法列表中删除Kerberos / GSSAPI():
session.setConfig( "PreferredAuthentications",
"publickey,keyboard-interactive,password");
以上是 使用JSch跳过Kerberos身份验证提示 的全部内容, 来源链接: utcz.com/qa/416415.html